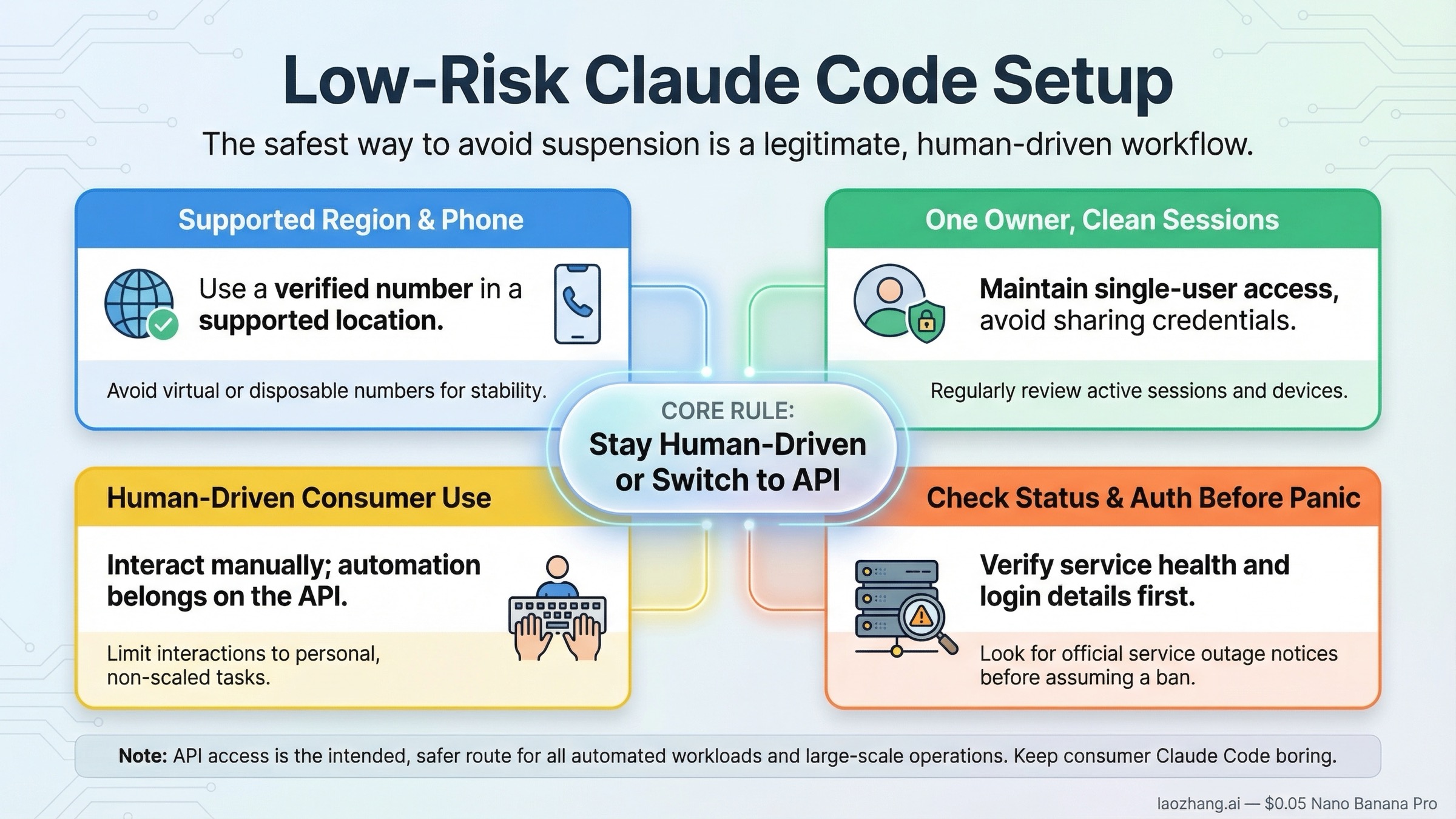
If you want the lowest-risk default for Claude Code, keep the setup boring: one supported region, one supported phone number you control, one human owner, and no shared logins or hidden automation behind a consumer Pro or Max subscription. Anthropic's current support pages, consumer terms, and troubleshooting docs all point in that same direction. If your real workflow needs background jobs, team access, or scripted agents, the safer move is to shift that workload to Anthropic API access instead of stretching a consumer plan past the job it was built for.
Start by sorting your problem into the right bucket before you react. organization disabled, login failures, borrowed-phone setups, unsupported-region workarounds, and old ANTHROPIC_API_KEY traces do not all mean the same thing. Separate policy risk, authentication mistakes, and ordinary product limits first; then fix the auth path, stop the risky account behavior, or move the automation layer to the API based on which bucket you are actually in.
| Risky behavior | Safer default | Why it lowers risk |
|---|---|---|
| Signing up from an unsupported location or with a borrowed phone number | Create and use the account only from a currently supported location with your own supported phone number | Anthropic's current signup and verification pages tie Claude access to supported locations and supported phone verification |
| Sharing logins, tokens, or letting other people use your account | Keep one owner per account and revoke old sessions when needed | Anthropic's Consumer Terms prohibit sharing account credentials or making the account available to someone else |
| Using a Pro or Max consumer account for headless automation or unofficial wrappers | Use Anthropic API access for automation, agents, and scripted workflows | Anthropic's Terms carve out API-key access as the proper path for automated use and restrict non-human consumer access |
Treating every organization disabled or login problem as a ban | Check /status, remove stray ANTHROPIC_API_KEY, and compare web vs CLI behavior first | Many lockouts are auth-path problems, usage resets, or status incidents rather than enforcement |
What actually lowers your Claude Code ban risk
Use Claude Code in the most literal, supported way possible. That means an account you personally control, created in a supported location, authenticated through official flows, and used by a human in the product surfaces Anthropic actually documents. Once you move away from that baseline, the risk does not rise because Anthropic is mysterious. It rises because you are leaving the safest part of the rulebook.
Anthropic's current Safeguards Warnings and Appeals page says accounts may be banned for repeated Usage Policy violations, account creation from an unsupported location, or Terms of Service violations. That page is short, but it gives the right frame. Your goal is not to guess what hidden machine-learning signal Anthropic might use. Your goal is to avoid the categories Anthropic has already put in writing.
For most readers, that leads to five practical rules.
First, do not build your Claude access on a region shortcut you cannot defend later. Anthropic's current Pro signup page says paid plans are only available to users physically located in supported locations, and it requires a phone number from a supported location to create an account. The current supported-locations page, checked on March 22, 2026, lists the United States but does not list mainland China. If you build your account around a borrowed region identity, your account may work for a while, but it starts from a weaker position than a genuinely supported setup.
Second, keep account ownership simple. Anthropic's Consumer Terms say you may not share your account login information, share your API key, or make the account available to anyone else. That makes informal "just let the whole team use my Max plan" logic much riskier than many users admit. If you need shared operational access, you do not need a smarter excuse. You need a different surface.
Third, keep automation on the API side. The same Consumer Terms say that, unless you are using an Anthropic API key or Anthropic explicitly permits it, you may not access the services through automated or non-human means. That clause is the clean dividing line many users skip. Human-driven Claude Code use with a supported subscription is one category. Bots, scripts, headless wrappers, and third-party harnesses built on consumer login tokens are another. If your real use case is automation, it is safer to use an API key and pay API rates than to pretend a consumer subscription is a general automation endpoint.
Fourth, do not turn ordinary product states into ban narratives. Anthropic's current Claude and Claude Code help pages explicitly describe usage-limit warnings, shared usage pools, login incidents, and auth conflicts. A five-hour usage reset is not a ban. A temporary auth incident is not a ban. A stale environment variable overriding your subscription is not a ban. Treating those like policy action is one of the fastest ways to start flailing into riskier behavior.
Fifth, keep your setup auditable. If you are ever asked to explain how you access Claude, the safest answer is easy to describe: my own account, my own phone verification, my own supported location, official login, no shared credentials, and API access only when I intentionally use API access. That kind of boring answer is exactly what you want.
Which behaviors Anthropic explicitly treats as high risk
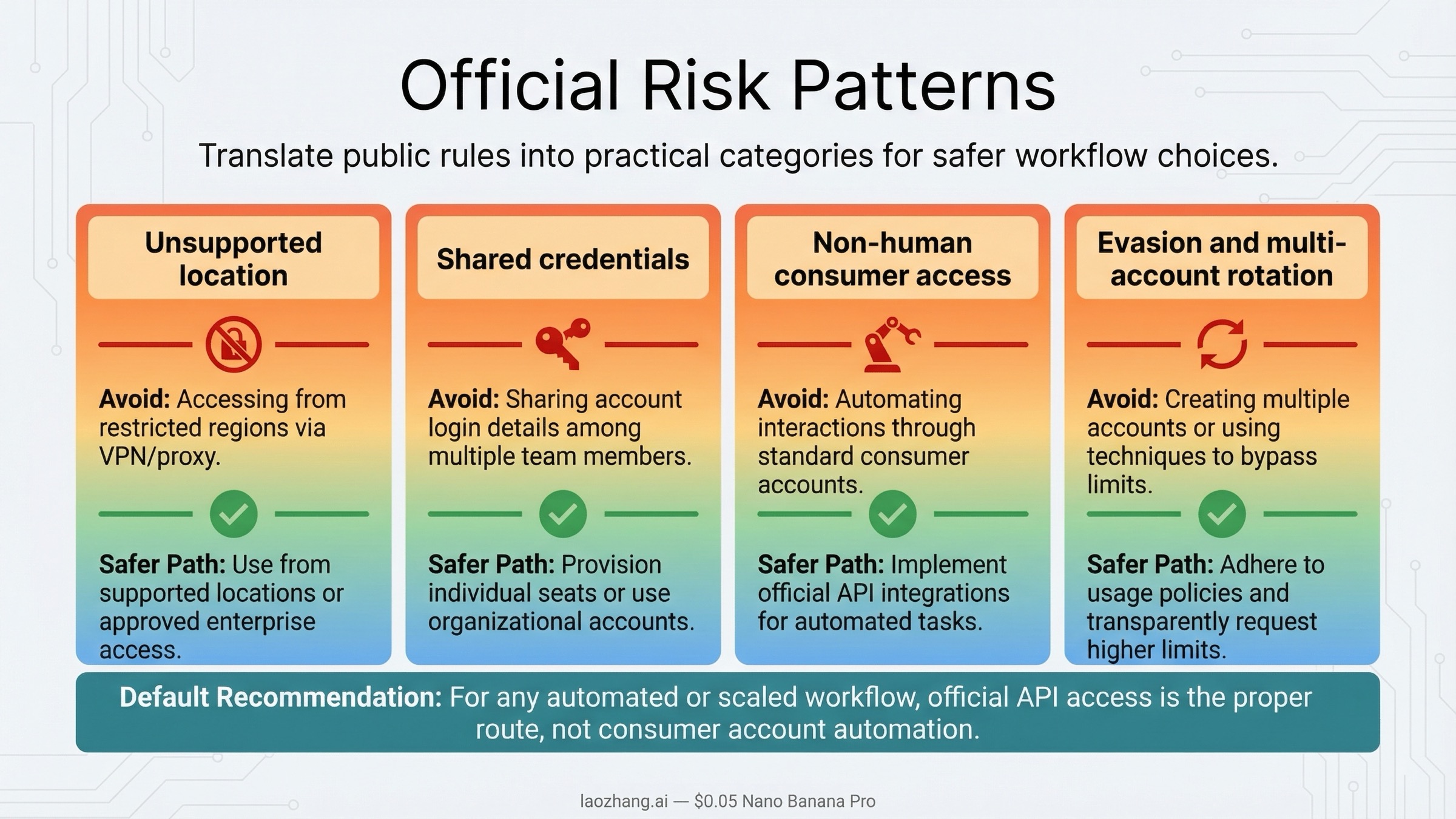
The official sources are more useful when you translate them into real behavior patterns instead of repeating policy labels.
The first official risk bucket is unsupported location. Anthropic's support pages do not say "some region tricks are tolerated if you are careful." They say the paid plans are only for users physically located in supported locations, and that account creation requires a phone number from a supported location. So the low-risk interpretation is strict: if your actual physical location is not supported, do not assume a foreign card, foreign number, or borrowed account wrapper makes the setup safe just because it worked once.
The second bucket is credential misuse. Anthropic's Consumer Terms forbid sharing logins and making the account available to someone else. That makes several popular "efficiency" habits much harder to defend than users think: letting a coworker use your Max account, copying browser sessions between machines you do not control, or keeping old Claude tokens active on shared systems. These are not neutral convenience hacks. They move your account farther away from the clean single-owner model Anthropic describes.
The third bucket is automated consumer-account access. This is where many developer workflows get sloppy. People tell themselves that they are still the user, so any wrapper they write is just "power-user usage." Anthropic's public terms do not frame it that way. The line they draw is not "light scripting versus heavy scripting." The line is whether you are accessing the service through automated or non-human means without the API-key exception. If you want background agents, scheduled tasks, tool chains, or multi-step autonomous execution, the safer move is to use Anthropic API access rather than a consumer subscription token.
The fourth bucket is evasion behavior. Anthropic's current Using Agents According to Our Usage Policy page is especially important here because it turns abstract policy into concrete examples. The page explicitly tells users not to create or manage multiple accounts to evade detection or circumvent platform safeguards. That is the strongest official public wording around multi-account evasion. It does not prove that every person with more than one account is automatically banned. What it does prove is that once the purpose becomes evasion or safeguard circumvention, Anthropic has already marked the behavior as out of bounds.
The fifth bucket is harmful or abusive agent use. The same agent-policy page lists surveillance, phishing, scaled abuse, coordinated harassment, and unauthorized account access as prohibited uses. Most ordinary Claude Code users are nowhere near those categories. But the lesson still matters: if your workflow starts to resemble abuse automation instead of coding help, you are walking toward the part of the rules Anthropic has made easiest to enforce aggressively.
Here is the practical translation:
| Pattern | Why it is risky | Lower-risk alternative |
|---|---|---|
| Unsupported-region signup or usage | Anthropic explicitly ties account access to supported locations and phone verification | Wait for official support in your region or use a product surface that is actually available to you |
| Shared account or borrowed credentials | Anthropic forbids making the account available to someone else | Give each human their own account, or move shared work to an org/API setup |
| Consumer subscription used as a bot or agent backend | Anthropic restricts non-human access unless you are using an API key or explicit permission | Use Anthropic API access for automation and integrations |
| Multi-account rotation to dodge limits or safeguards | Anthropic explicitly warns against multiple-account evasion in the agent-policy page | Reduce usage, pay for the right tier, or move the workload to the API |
| Ignoring warnings and continuing the same behavior | Anthropic says warnings are part of its safeguards process | Stop, review the policy issue, and change the workflow before pushing further |
What matters here is not fear. It is classification. If you can look at your workflow and say, "This is a normal individual human using Claude Code through official login," you are in a safer place than someone whose setup depends on region mismatches, hidden automation, and shared credentials.
Build a low-risk setup: region, phone, auth, and sessions
The safest account is not just policy-compliant in theory. It is operationally clean.
Start with the basics. Anthropic's current phone verification page says there is no way to skip phone verification and that you must have a phone number from a supported location to create and use a Claude account. That means "borrow a number, get through signup, and figure it out later" is not a durable plan. If the number belongs to someone else, if it was used on another account, or if you may lose access to it later, the account gets harder to manage safely over time.
Then clean up your login surface. Anthropic's current How do I log out of all active sessions? page says web sessions last 28 days and refresh automatically with activity. It also lets users revoke Claude Code authorization tokens from Settings > Claude Code. That matters for prevention because many people think of suspension risk only in terms of prompts or geography. In practice, an old device, shared laptop, or forgotten authorization can create its own mess. If you no longer control a device or you suspect someone else may still have access, clean up sessions first.
Next, decide whether you are using Claude Code as a subscription surface or an API surface. Anthropic's current Using Claude Code with your Pro or Max plan article says Claude Code can use the same credentials as Claude and that /login switches you back to the correct subscription path when needed. But it also warns that if ANTHROPIC_API_KEY is set, Claude Code will use the API key instead of your subscription. Anthropic's dedicated environment-variable guide goes even further: to use Claude Code with your subscription, keep ANTHROPIC_API_KEY unset.
That is one of the most important preventive habits in this entire article. Many users think they are operating on a personal Max or Pro plan when the terminal is actually pointing at an old API key from work, school, or a disabled organization. Once that happens, the CLI can throw confusing errors that feel like a ban. The risk is not only billing confusion. The bigger risk is that the user now misdiagnoses the account state and starts reacting badly.
The official safer pattern is simple:
- if you want subscription usage, keep
ANTHROPIC_API_KEYunset and check/status - if you want API automation, set the API key deliberately and treat the workflow as API usage, not as a hidden extension of your consumer subscription
- if you are switching back and forth, do it consciously rather than leaving stale credentials behind in shell startup files
This is also why shared-device discipline matters. An account that has been cleanly logged out, with tokens revoked and environment variables understood, is much easier to reason about than an account that has touched multiple teammates' laptops, old shell configs, and random wrapper tools.
Do not mistake heavy usage, outages, or auth bugs for a ban
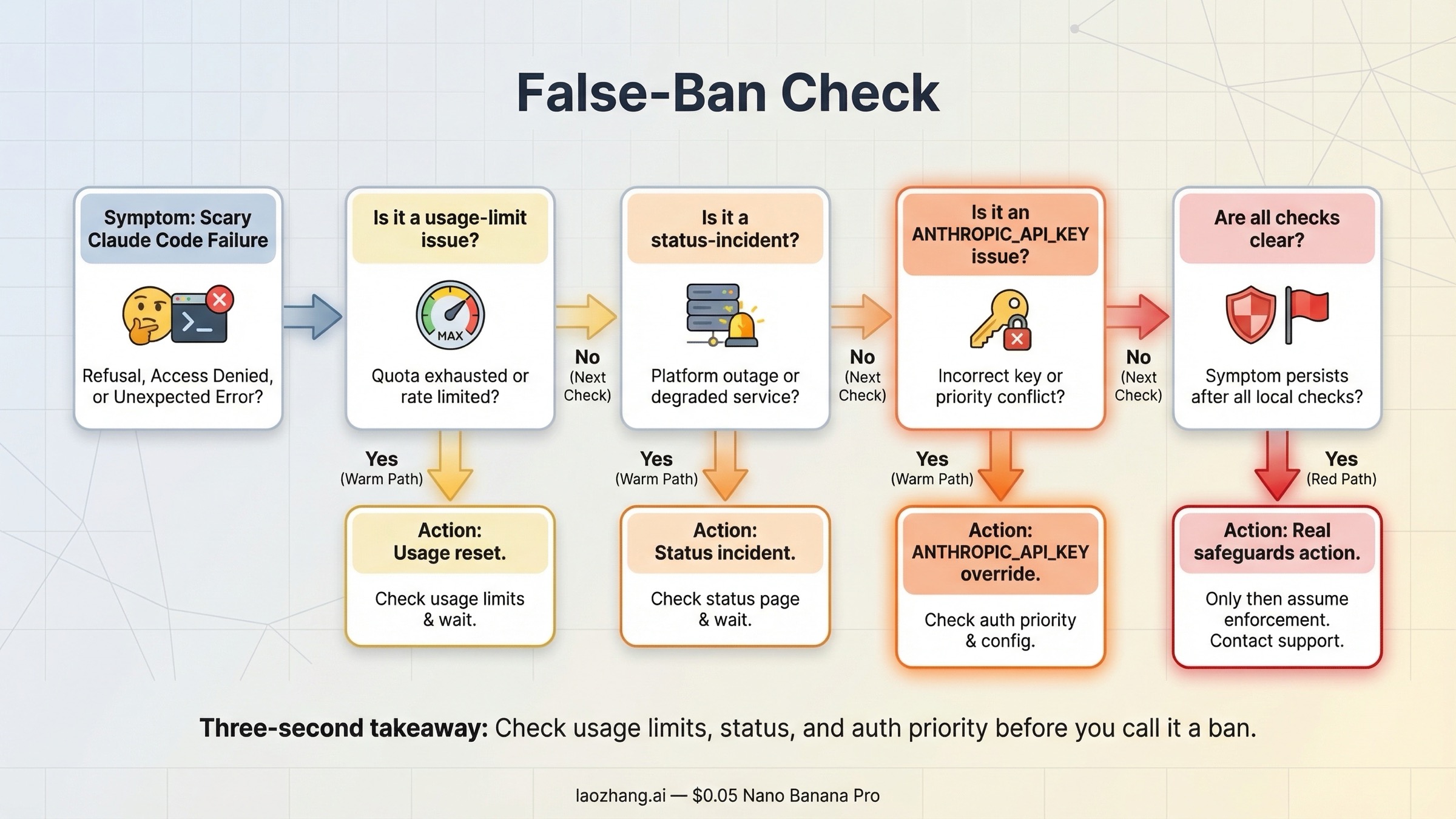
Bad advice usually starts when people treat every scary-looking account state as proof of a ban, even when the underlying cause is only usage pressure, auth mistakes, or a temporary platform incident.
Anthropic's current How do usage and length limits work? page says usage limits across claude.ai, Claude Code, and Claude Desktop count toward the same usage limit. The current error-message guide says usage-limit warnings appear before the blocking five-hour reset message. Heavy use, then, is not itself evidence of policy action. Sometimes it is just heavy use.
The same error-message guide also says that if you see a generic login error, you should ensure you are not using a VPN, disable browser extensions, clear cookies, and check the status page. That wording matters because users often overstate what the page says. Anthropic is not publicly saying "VPN use automatically gets you banned." What it is saying is narrower: if login is failing, one of the first troubleshooting steps is to test without a VPN. That is the conservative way to write about it.
Status incidents matter too. As of March 22, 2026, Claude Status showed all systems operational, but the recent incident history included March 18 and March 19 events that affected authentication across Claude surfaces, including Claude Code login or logout behavior. If you get locked out during a live auth incident, the right answer is not to create a new account, rotate regions, or assume you were individually targeted. The right answer is to check the status page and wait for a clearer signal.
There is also the This organization has been disabled trap. The official Anthropic pages now explain the authentication priority, but the community pain around this issue is still real. In GitHub issue #8327, a Claude Code user documented a reproducible case where an old ANTHROPIC_API_KEY from a disabled organization overrode a valid Max or Pro subscription and produced the organization has been disabled error. In issue #5088, another user described paying for Max 5x and then seeing the same error after payment. Those issues are not policy authorities, but they prove how easy it is for users to misread an auth-path problem as a full suspension.
Use this table when something goes wrong:
| What you see | What it usually means | What to do first |
|---|---|---|
Approaching 5-hour limit or a reset-time message | Normal usage-limit behavior | Check /status, wait for reset, or use the correct paid option for more usage |
| Generic login error | Browser, extension, VPN, cookie, or incident problem | Test without a VPN, clear auth state, and check status |
This organization has been disabled in Claude Code while web Claude still works | Often an API-key override or disabled org credential | Unset ANTHROPIC_API_KEY, relogin, and compare web vs CLI again |
| Web and CLI both failing during a live status incident | Product outage or auth incident | Wait for status resolution before escalating into appeal logic |
| Warning email or explicit suspension notice | Real safeguards or policy action | Stop the risky behavior and move to the evidence-and-support path |
This table is where many weaker pages fail. They jump from "error happened" to "ban happened." That is not good enough for a user who needs the right next move.
What to do after a warning or suspicious lockout
The right reaction to a warning is not panic. It is containment.
Anthropic's safeguards page says warnings are part of the current safety process and that users may be warned when Anthropic believes prompts are violating the Usage Policy. If you get a warning, do not keep testing the edge by slightly rephrasing the same behavior. Stop and review what you were doing. If the workflow involved mass automation, questionable data collection, shared access, or a region shortcut, assume the system noticed the general pattern rather than a single magic phrase.
If the lockout is suspicious but not yet clearly a ban, work in this order.
- Check the live status page.
- Compare web Claude and CLI Claude Code behavior.
- Remove
ANTHROPIC_API_KEYif you intended to use your subscription. - Reauthenticate with the official login path.
- Revoke old Claude Code tokens or all sessions if device hygiene is part of the problem.
- Only after that decide whether you need the safeguards appeal path or normal support.
If the account really is suspended, use the official support and appeal route. If the question has already moved from "How do I avoid this?" to "I paid and got locked out, what about my refund?", the better next step is our sibling guide: Claude Code Ban Refund: What Happens After Suspension?. That page is for reactive billing and refund triage. This one is deliberately about prevention.
You should also preserve evidence before retrying too many things. Save the error text, the time it happened, whether web and CLI both failed, whether ANTHROPIC_API_KEY was set, and whether the status page showed an incident. Good evidence does not just help support later. It also prevents you from rewriting the story in your own head after a stressful hour of trial and error.
The biggest preventive lesson here is behavioral. Warnings and weird lockouts are moments to get simpler, not more creative. If your first instinct is to rotate accounts, change regions, or borrow a new login, you are probably moving in the wrong direction.
When you should switch to the API or another tool instead of pushing a consumer account
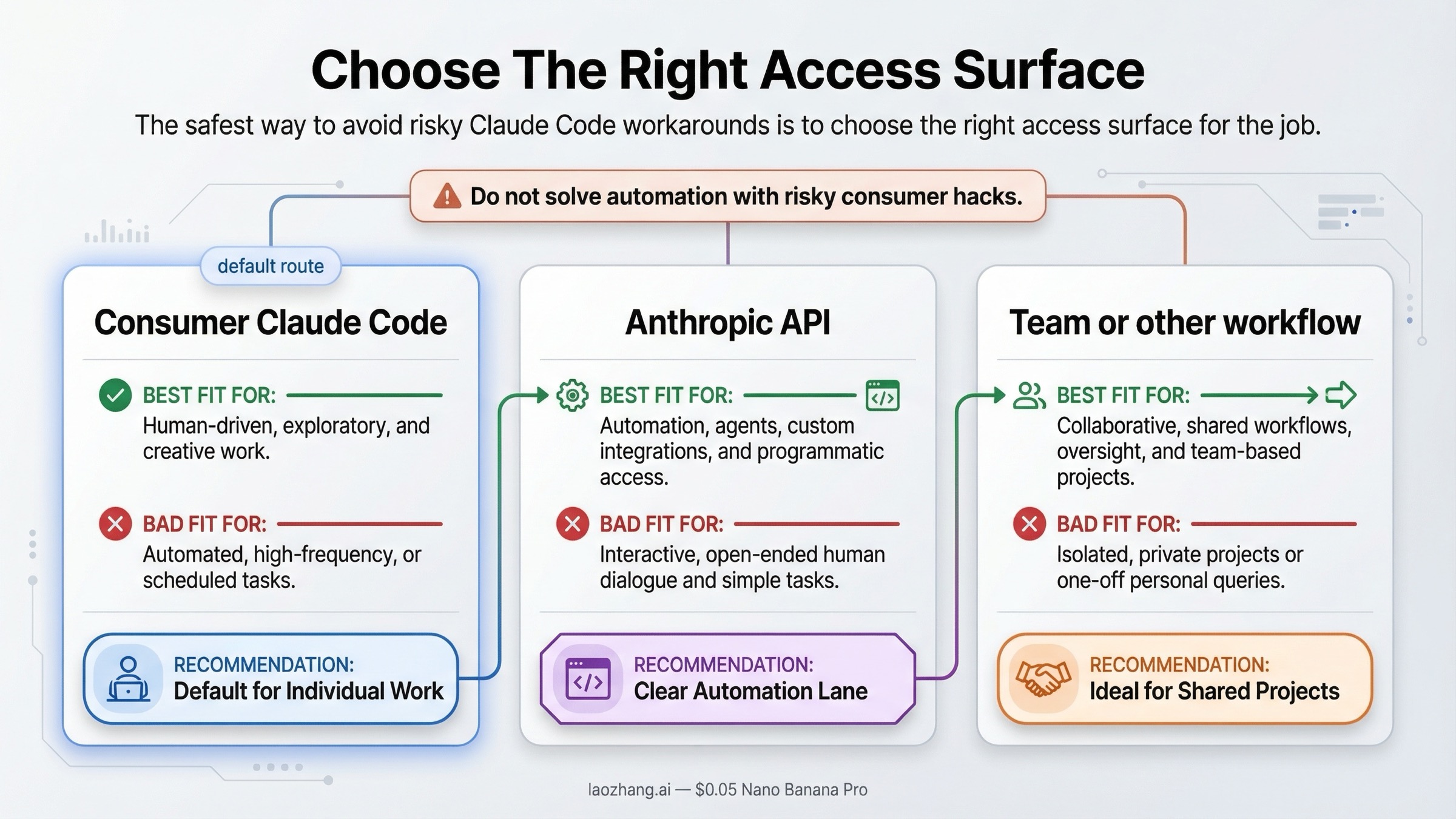
Some readers do not actually have a "ban avoidance" problem. They have a product-surface mismatch.
If your real requirement is one or more of the following, you should seriously consider moving off a consumer subscription workflow:
- headless automation
- background agents
- scheduled jobs
- tool chains that pass credentials between services
- shared operational access for a team
- high-volume usage where rotating consumer accounts feels tempting
That is not because Anthropic is hostile to serious users. It is because consumer Claude access and Anthropic API access are not the same thing. Anthropic's own terms make that distinction explicit. The safer path for automation is the API path.
For many developers, that shift also improves clarity. Subscription access is good when you want a human-driven Claude and Claude Code workflow under one account. API access is better when you need programmable control, auditable billing, or a workflow that would otherwise push you toward consumer-account shortcuts that start looking like policy violations.
If cost or volume is the reason you started thinking about multi-account rotation or third-party wrappers, solve that problem directly instead of hiding it. A few pages in this repo can help:
- Claude Code Pricing and Lower-Cost Options in 2026
- Claude API Pricing Guide
- Claude API Quota Tiers and Limits
- How to Install Claude Code
There is also a practical mindset shift hidden here. The goal should not be "How do I keep forcing Claude Code to work through whatever route is still open?" The goal should be "Which access surface best matches my actual workflow while staying inside the published rules?" Once you ask the second question, the path is often much cleaner.
FAQ
Do VPNs, account sharing, or multi-account rotation create ban risk?
Anthropic's current public error-message guidance does not say that a VPN automatically causes a ban. What it does say is that if login is failing, you should test without a VPN before assuming something worse happened. That is a troubleshooting instruction, not a published zero-tolerance ban rule. The safer takeaway is practical: do not make login and region behavior harder to explain than it already is.
Account sharing is much clearer. Anthropic's current Consumer Terms say you may not share your account login information or make your account available to someone else. And Anthropic's current agent-policy page says not to create or manage multiple accounts to evade detection or circumvent safeguards. So if the workflow depends on rotating accounts to dodge limits or putting multiple humans behind one consumer account, the safer answer is no: do not do that.
Can I use a Claude Pro or Max subscription for agent frameworks and automation?
Not if the workflow depends on automated or non-human consumer-account access. Anthropic's current Consumer Terms make API-key access the safe exception for automation. If the workflow is truly programmatic, treat it as an API use case rather than trying to smuggle it through a consumer subscription.
When should I stop forcing Claude Code and move to the API?
Move to the API when your real need is automation, scheduled tasks, multi-agent orchestration, shared operational access, or usage patterns that keep pushing you toward account-sharing or multi-account shortcuts. The more your workflow looks like infrastructure, the less appropriate a consumer subscription becomes.
Final answer
If you want the lowest-risk answer to "How do I avoid a Claude Code ban?", it is this: use Claude Code as an individual human on a legitimately created account in a supported location, keep your auth path clean, do not share credentials, do not automate consumer access, and do not confuse usage limits or auth incidents with enforcement. If your workflow needs automation, team use, or high-volume orchestration, move to the API instead of improvising around a consumer subscription.
That answer is less exciting than ban folklore. It is also much more durable.